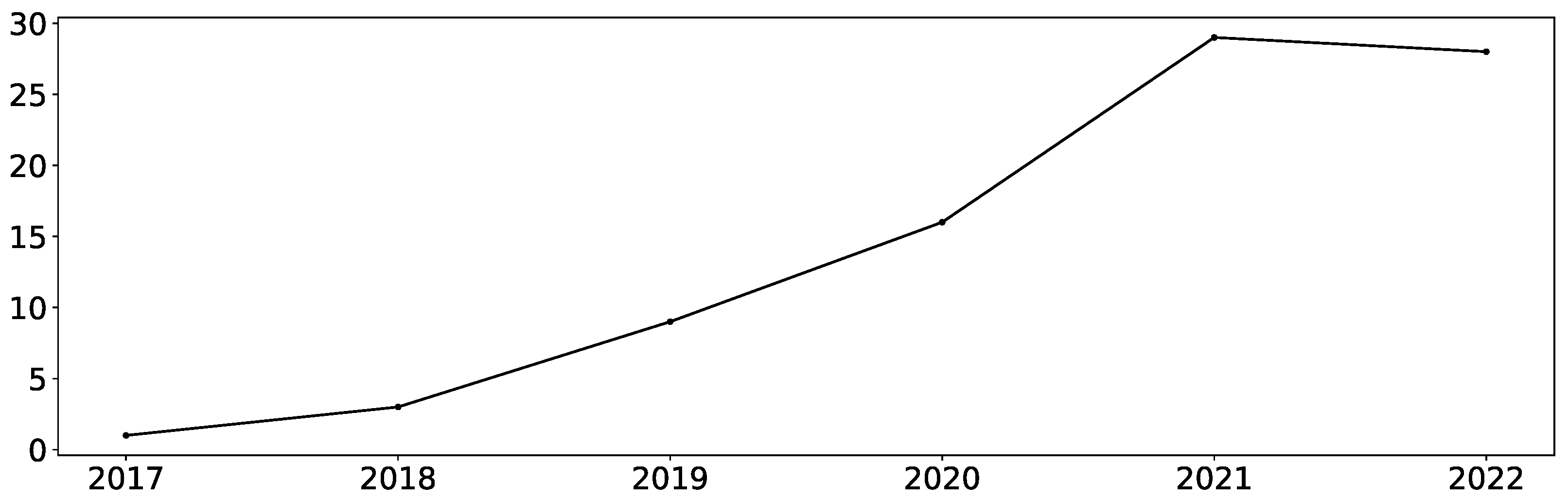
Electronics | Free Full-Text | A Survey of Bit-Flip Attacks on Deep Neural Network and Corresponding Defense Methods

The Story of Rowhammer - Secure Hardware, Architectures, and Operating Systems Keynote - Onur Mutlu - YouTube

Memories, ACEs, Frye, Anonymity -- AN Examination of Procedural and Substantive Challenges under New York's Child Victims Act Hon. Richard A. Dollinger, - ppt download
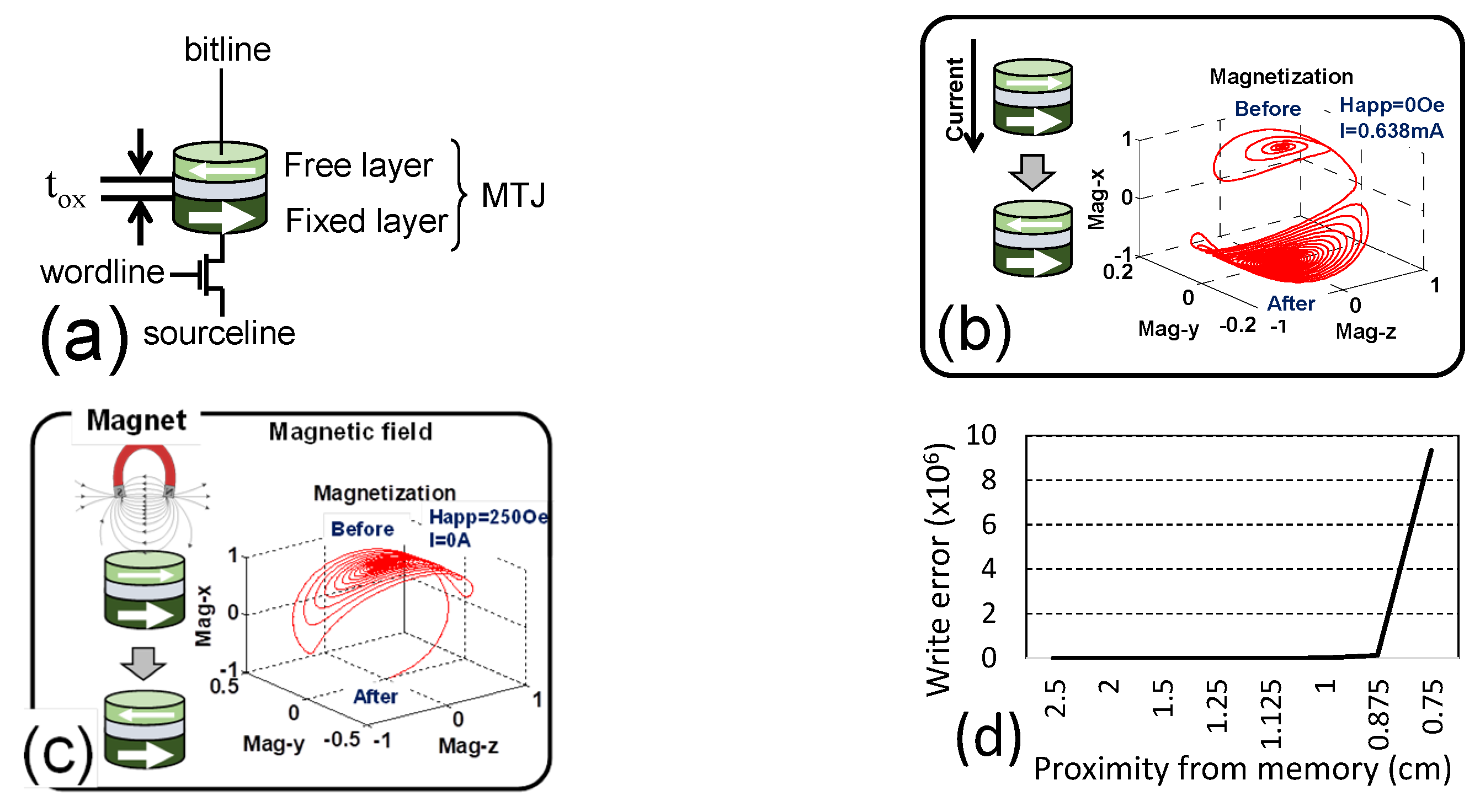
JLPEA | Free Full-Text | Comprehensive Study of Security and Privacy of Emerging Non-Volatile Memories